The best explanation for why Windows is
slow that I’ve heard was an explanation of ‘building funnels” from a
state highway engineer. Roughly: “That commuting route is beyond planned
capacity. Yes, we could add lanes to it and increase the capacity, fit
more cars, and even increase the speed limit if we make it limited
access. No problem there. But these commutes don’t end in highways, they
end in neighborhoods, in areas we can’t control, county roads and other
states. So adding capacity encourages more use, which results in
building funnels at both ends of the commute where the extra lanes are
taken away, and the funnel and resulting merges back up the traffic.”
And then, darker, “Sure, we could co-ordinate work with other states to extend things, but why should we invest anything to encourage building in areas that don’t give us any tax revenues but add to our highway costs? And worse, developers build homes on a much shorter timeline than we can plan state highways, let alone fund them and build them.”
Of course, the people who live alongside these racetrack routes, the worst of the commuter single-lane state highways, have things to say on these topics.
But back to technology. This is the classic Windows stupidity of running background tasks when the system is slow, but not in sleep mode. So let’s set a service, we’ll call it “Street Cleaning” just to make it non-techy, and say “We don’t want that to run during rush hour. Let’s have it run whenever the controller sees that traffic is low. Can’t do it when there is no traffic at all, because we’re turning off the streetlights when nobody’s on the road. So when the streetlights come on, check recent traffic, see that it’s zero, and start cleaning the streets. Excellent.”
This, of course, turns on the streetlights based on a motion sensor, and sequentially starts “Street Cleaning” at the moment that a car enters the parkway. Or triggers some service to start doing complex background stuff because you woke the computer and started typing. Or set twenty to fifty services to start running and phoning home for updates when the computer is first turned on. Which leads most users to start the computer, and then start the coffee pot, and not come back until both computer and operator have been thoroughly woken up.
Preventing Startup Buildup
Old computers aren’t always slow because they’re old. If they were not budget computers on day one, they shouldn’t act like junk in year three. If they do, and the hardware tests out OK, the remaining cause for ‘slow’ or ‘erratic’ is generally “too much software trying to run at the same time.” That’s a traffic condition, background junk that does not need to be there. Some of it is malware, and a lot of it is just un-needed junk that is not remotely evil. But all auto-starting software adds to startup time.
So, to prevent that, you have to avoid software that adds auto-starting stuff to the system. I’ve told many of you this before, here it is again. It’s important: When you install software, always choose the Custom install. Always. Even if you have no plans to change anything, even if you’re afraid of even touching it. Always. And then read the screens during the setup, and pay attention to the options. The default options will work, they’re tested heavily, but they were not tested on every possible computer configuration.
What you’re looking for in those option screens are the choices that mention “Also install this…” or “Start with Windows”. Those always require a moment of asking why would that be a good thing? Why allow that? Why allow a Hewlett Packard printer to run a program at startup that phones home to Hewlett Packard for a new driver, waiting for an overloaded server to respond, for the life of the computer? Think about that–not the life of the printer, and not the life of the printer warranty, but forever. Now multiply that by a dozen, and that’s a typical HP printer setup.

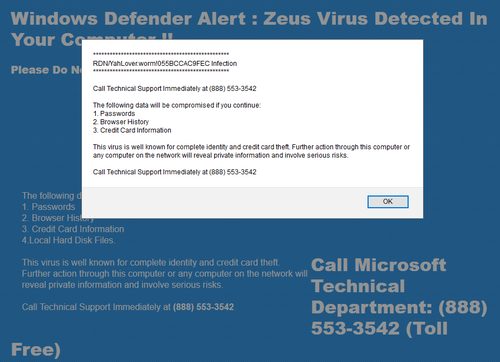
Now all of these startup items are not available to “just say no” to during setup, and I can follow up later during a tuneup to remove the useless autoplays, but for those choices that appear, if you won’t need a listed feature, don’t install it. And if it’s a third-party program, as in “we also recommend,” that’s a malware installation tactic. While not all software that arrives in that way is evil, you didn’t go looking for it, so you don’t need it, so don’t let it install.
There are a lot of small utility programs that suggest ‘Run with Windows.’ OK, let’s see, it’s a little utility that you have never needed before, that converts something to something else, and it wants to start with Windows because you will need it every day, forever. No. Just say no.
As the Printers Die
Reminder: If you bought a new printer to replace another, go to Control Panel, Uninstall a program, and remove the software that installed with the former printer. Also check the printer list, in Settings, Devices, Printers & scanners, and remove the old driver there. It’s easier to do that before installing the new software, especially if the new and old printers are the same brand. The rule is like any other cleanup rule: Demolition before rebuilding. Make space before organizing. Remove that old plumbing before adding the new pipes. Or wires, or software. That helps you identify the old stuff, wipe it out before adding the new stuff.
Other old software should also be removed. Any program that has an annual version can cause problems, so don’t allow them to build up forever. If you will never use these products past, say, year 3, then delete the “three years back” version when you add the latest version.
Do Hard Drives Fill Up?
The answer is generally “not from saving documents.” But software can fill them, as can video editing in high resolution, or Windows errors that cause log files to never ever go away–that’s currently a recurring issue in Windows 7. If there is very little software on your system, but there are ‘full’ warnings in Windows, it can be the log files–call for a cleanup.