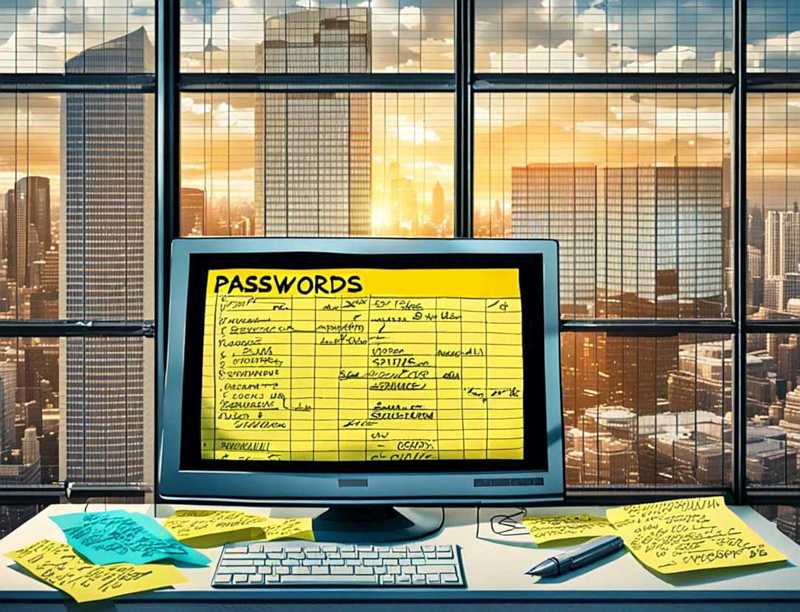
These phish attempts are worse, much worse, for those of you who insist on using one password everywhere and forever. Again, once a phishing attack lands a password and user account login, or worse, an email login that can be used to confirm logins, these thieves will try using those logins to the top 20 to 50 banking and ecommerce sites, and see what accounts they get access to. AI will make this worse…
Continues in the free March 2026 PC Updater News, or read back issues here.